Hey there, long time no see!
Sorry for going dark on you for the last 5-6 weeks. I had a few folks check in on me to make sure I was okay, and I appreciate that, but don’t worry, I’m good. I made an intentional decision to deprioritize Disclosed because I saw a huge opportunity that I believed to be super time-bound, and I jumped on it.
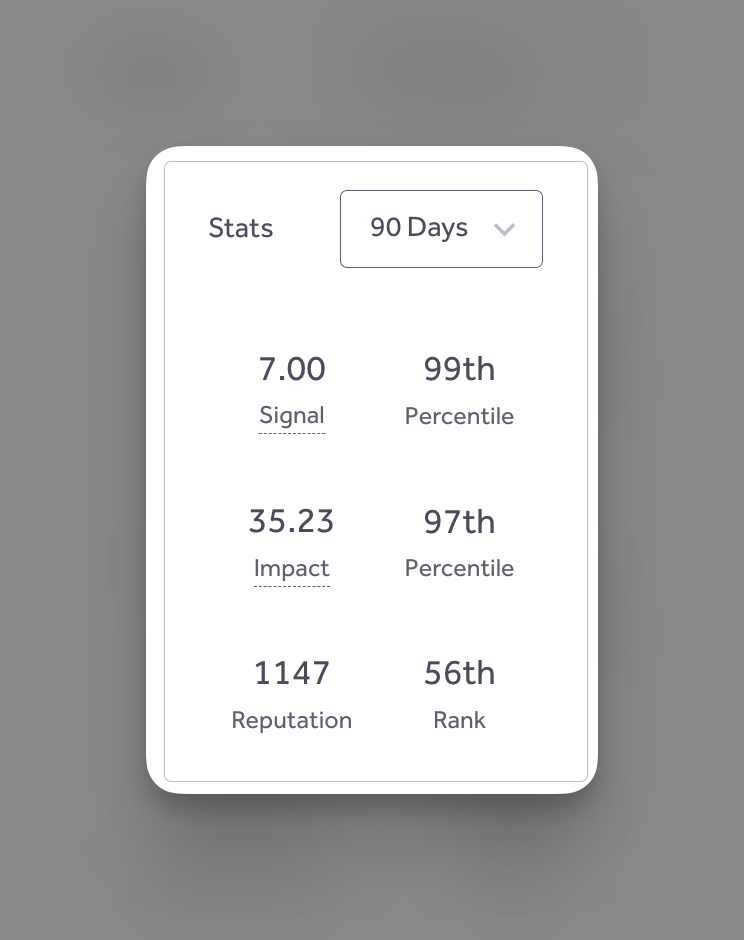
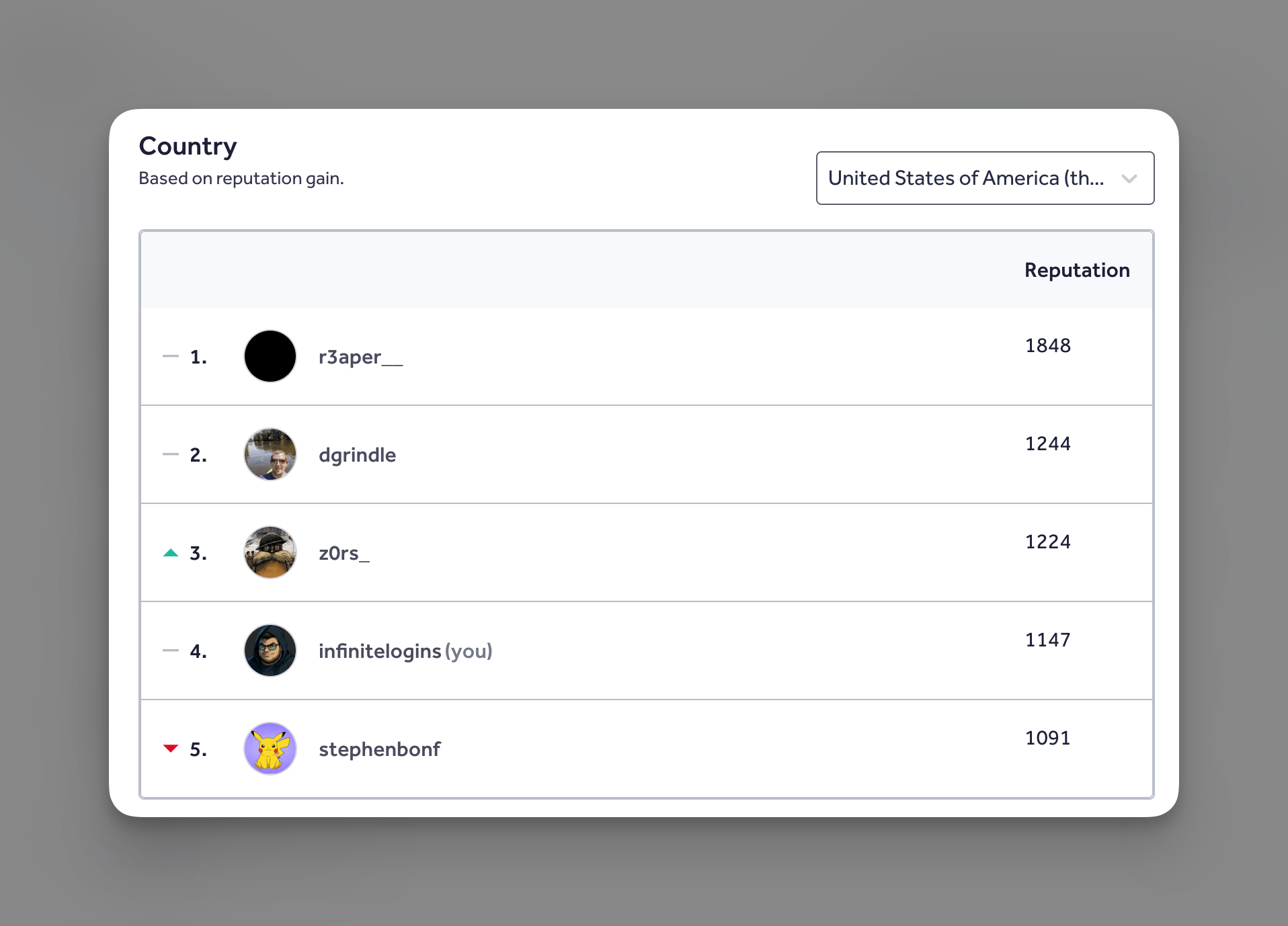
I’ve spent ALL of my free time over the past 6 weeks building out my own autonomous bug bounty hunting system and have been seeing pretty awesome success with it, climbing the HackerOne leaderboard to top 60 for the last 90 days and top 5 in the US as of this writing: metrics that I honestly never thought I would personally hit.
I’ve been completely obsessed with building this and have learned a monumental amount about building scalable AI systems these past few weeks. I have a lot of “secrets” that I wouldn’t want to share yet, but if you’d like to hear more from me about this, let me know. Maybe I can be convinced to share some things. I also encourage you to reach out to me directly if you’re interested in collaborating.
All that said, there is SO MUCH to cover from the last 40+ days since my last issue of Disclosed. This particular post will be significantly larger than normal since I’m trying to consolidate the important stuff from over a month of content that I usually produce weekly.
That said, there’s some real gold in here, so I highly recommend you take the time to read through these.
Let’s dive in.

Self Promo: I’m available for 1:1 calls if you want to chat about bug bounty, career growth, community building, or anything else you think I can help with. You can book time with me here.

DEF CON 34 Bug Bounty Village CFP Opens (Deadline: May 15) [𝕏 Tweet]
by Bug Bounty Village
The DEF CON Bug Bounty Village is taking talk submissions for DEF CON 34, with a May 15 deadline. The CFP call outlines what they’re looking for and where to submit proposals for this year’s village program.
HackerOne Publishes a Bug Bounty Program Maturity Framework [𝕏 Tweet]
by HackerOne
HackerOne published a program maturity framework that sets expectations for how bounties should run, including researcher comms, payout timelines, scope quality, and disclosure posture. It’s positioned as a baseline for operational standards that programs can benchmark against.
Valentino Massaro Wins MVH at Google LHE in Seoul
by Valentino Massaro (@valent1nee)
Google Crowns a new MVH in Seoul.
StarStrike Team Wins 2nd Place at Google LHE in Seoul
by Ciarán Cotter (@monkehack)
Starstrike takes 2nd Place MVH at Google's Seoul Live Hacking Event, plus Most Creative and Most Novel Prompt Injection awards. The team — STÖK, Vitor Falca, and Ciarán Cotter — now has back-to-back 2nd place finishes at Google LHEs.

NahamSec Hosted a Bug Bounty Village at BSidesSF [𝕏 Tweet]
by Ben Sadeghipour (@NahamSec)
NahamSec ran a bug bounty village presence at BSidesSF and shared the event details for attendees.
Have something you want to Spotlight? Tell me.

Bugcrowd Tightens Enforcement Against Low-Quality “AI Slop” Reports [📓 Blog]
by Bugcrowd
Bugcrowd outlined new policy and enforcement changes aimed at reducing automated and low-signal submissions that are inflating triage queues. The update includes stronger penalties for report farming, account suspensions after repeated invalid reports, and additional controls to curb automation-driven bulk submissions.
Node.js Pauses Its Security Bug Bounty Program [𝕏 Tweet]
by Node.js
The Node.js project announced it is pausing its security bug bounty program while keeping security reporting and coordination processes intact. Researchers should continue to use the standard reporting channels referenced in the announcement.
OpenAI Launches a Safety Bug Bounty for AI Abuse and Misuse [𝕏 Tweet]
by OpenAI
OpenAI announced a Safety Bug Bounty that expands beyond traditional security issues into AI-specific abuse and misuse scenarios across its products. The program aims to centralize reporting for safety-impacting behaviors and operational risks tied to model usage.
T-Mobile Expands Supplemental Assets on Bugcrowd (~100 Targets) [𝕏 Tweet]
by the_IDORminator (@the_idorminator)
T-Mobile reportedly added roughly 100 sites to its supplemental assets on Bugcrowd. The post suggests prioritizing the new additions and using quick recon pipelines (e.g., GAU/Waymore + dorking) to surface endpoints worth manual follow-up.
Meta Bug Bounty Partners with PortSwigger (Burp Pro Licenses) [📓 Blog]
by Meta Bug Bounty
Meta announced a partnership with PortSwigger, starting with Burp Suite Pro licenses for select researchers in Meta’s HackerPlus Silver leagues. The post is community/program support focused and does not include technical vulnerability details.

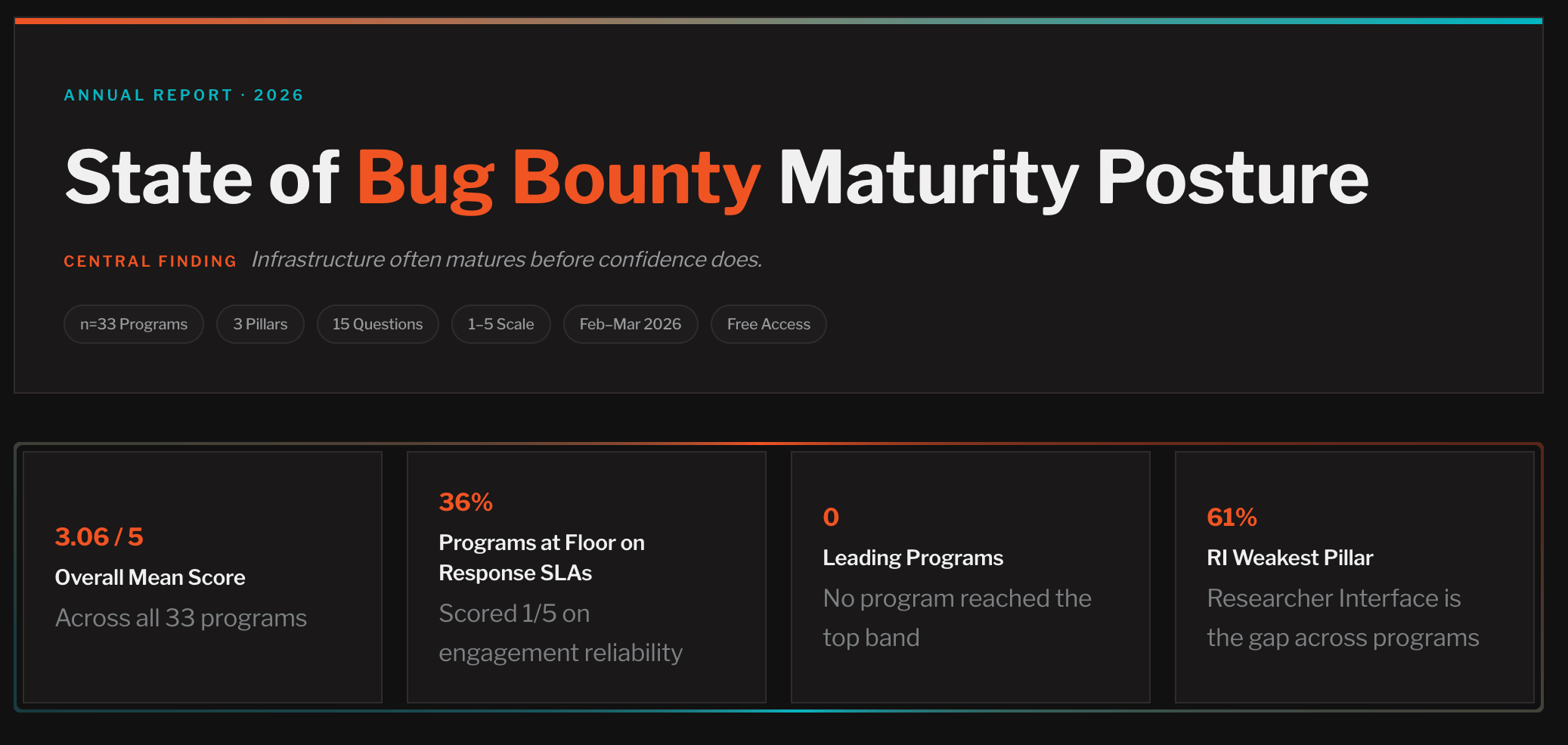
by Bug Bounty Maturity Framework (@BBMFramework)
The BBMF, an independent maturity diagnostic built by Steve Hernandez (ex-HackerOne), published its inaugural research report based on 33 program assessments.
Google VRP Requires Minimized PoCs and ASAN Traces for Memory Bugs [𝕏 Tweet]
by zerodayalpha
A shared update notes Google VRP now requires minimized proofs-of-concept and ASAN traces for memory-safety reports. This materially changes submission requirements and raises the bar on the artifacts needed for a valid report.
Bugcrowd Achieves FedRAMP Moderate Authorization [📓 Blog]
by Bugcrowd
Bugcrowd announced FedRAMP Moderate authorization (sponsored by CISA), enabling federal agencies to use its platform under government security requirements. This is a compliance and procurement milestone rather than a technical release.
The Internet Bug Bounty (IBB) program has paused new submissions effective March 27, citing a fundamental shift in the discovery-to-remediation balance driven by AI-assisted research. The program, which splits rewards 80/20 between discovery and remediation, says AI tooling has expanded vulnerability discovery faster than open source maintainers can remediate — and they need to restructure incentives accordingly. Active submissions will continue through normal review and payout. HackerOne will continue providing qualifying open source projects with free access to their Community Edition platform.
HackerOne Updates Code of Conduct To Introduce AI-assisted Research & Submission Standards
by HackerOne
HackerOne has added formal AI research guidelines to their Code of Conduct. The policy permits AI tools across the entire workflow — recon, discovery, PoC development, and report writing — but draws clear lines: researchers remain fully responsible for all AI-assisted output, must validate every finding, and must provide reproducible proof-of-concept with real-world impact. Autonomous and semi-autonomous agents are explicitly covered, with researchers accountable for staying within program scope, rate limits, and testing restrictions.
Did I miss an important update? Tell me.

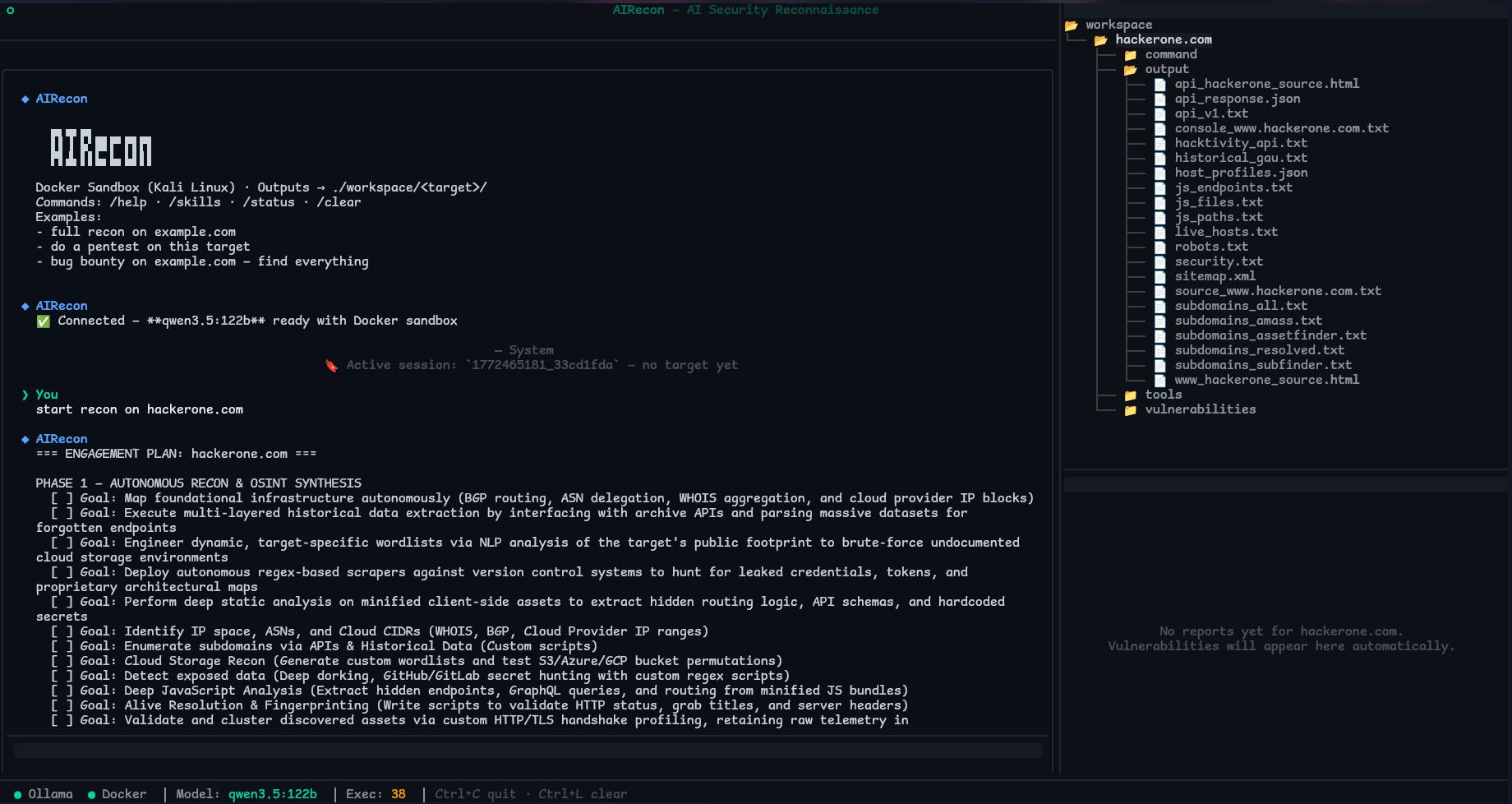
AIRecon: Offline Autonomous Recon/Exploitation Agent (Ollama + Kali Docker) [🛠️ Tool]
by pikpikcu
AIRecon is an autonomous security agent that pairs a self-hosted Ollama model with a Kali Linux Docker sandbox and a TUI workflow for recon, analysis, exploitation, and reporting without cloud APIs. It also supports proxy tooling integrations and a structured pipeline intended to reduce manual glue between recon output and exploitation attempts.
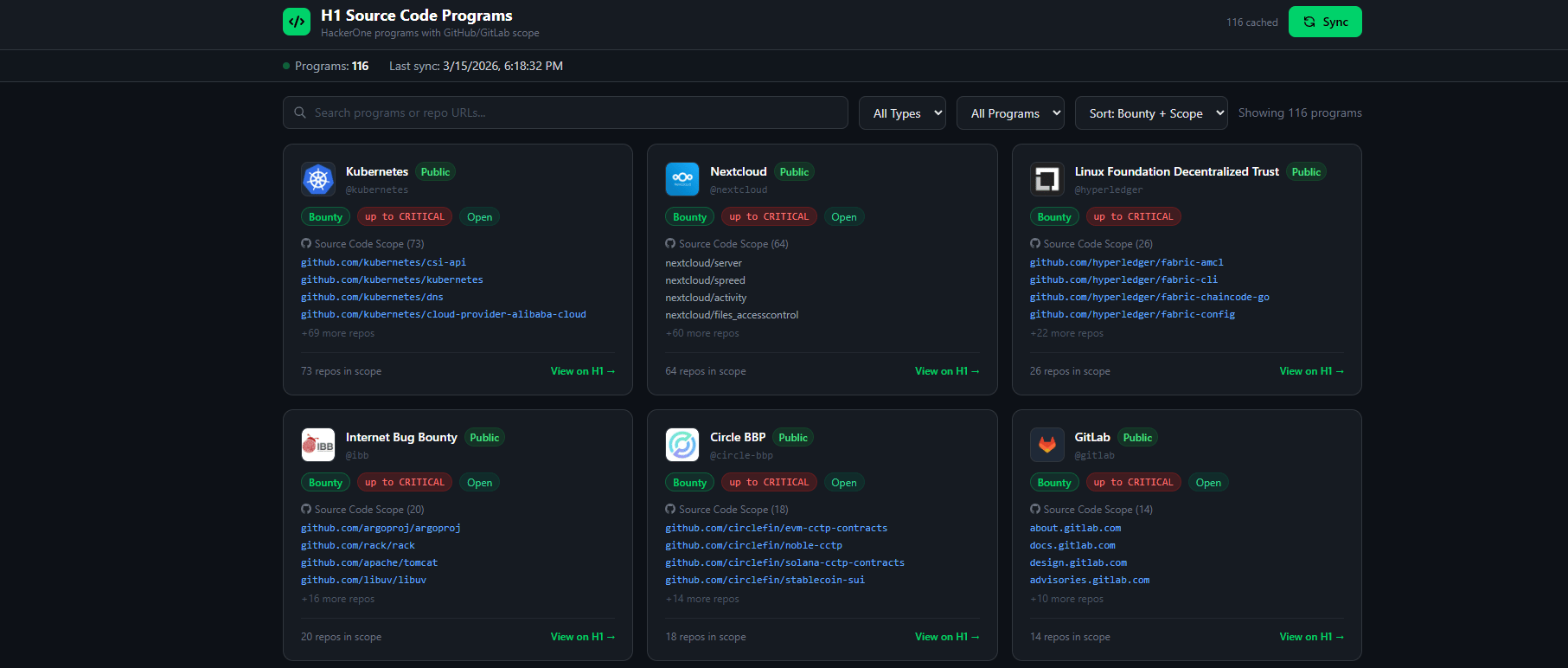
sourceCodeProgramsH1: Find HackerOne Programs with Source Code Repos in Scope [🛠️ Tool]
by Clover (@actuallyclover)
This app aggregates HackerOne programs that include GitHub/GitLab/Bitbucket repositories in structured scope, making it easier to target code-review surfaces. It syncs via the HackerOne API, caches results, and provides a searchable UI with direct links to in-scope repos.
h1-brain: MCP Server That Connects AI Assistants to HackerOne Data [🛠️ Tool]
by Patrik Fehrenbach
h1-brain is an MCP server that lets MCP-compatible assistants query HackerOne scope and report history, with local indexing into SQLite and an optional dataset of disclosed reports for enrichment. It’s designed to generate hunting briefs from prior findings and current program scope to speed up targeting and triage.
hackerone-mcp-server: Unofficial MCP Server for HackerOne (Reports, Scope, Submissions) [🛠️ Tool]
by SickSec (@OriginalSicksec)
This unofficial MCP server exposes HackerOne API operations to Claude Code (or other MCP clients), including report search, scope lookups, and submission/comment workflows. It adds practical safeguards like pagination, caching, and rate-limit handling to make automation against HackerOne data more reliable.
Hyoketsu: Offline DLL/JAR Identification for Reverse Engineering Triage [🛠️ Tool]
by AssetNote (@assetnote)
Hyoketsu fingerprints DLLs and JARs offline to separate known third-party libraries from custom code using token extraction and hash-based matching against large Maven/NuGet datasets. It’s useful for speeding up reversing and source review by focusing effort on unknown binaries that are more likely to contain app-specific bugs.
Burp Bounty Lab: Local Vulnerable App to Validate Burp Bounty Scanner Profiles [🛠️ Tool]
by BountySecurity
Burp Bounty Lab is an intentionally vulnerable, Dockerized target that simulates 100+ endpoints across common bug classes to verify Burp Bounty Pro profiles against known patterns. It’s geared toward reducing false positives/negatives in custom scanning setups before running profiles against real targets.
bugSkills: Turn Resolved HackerOne Reports into Reusable AI “Skills” [🛠️ Tool]
by BehiSecc
bugSkills pulls triaged/resolved HackerOne reports, masks sensitive identifiers, and uses an LLM to extract repeatable methodology into per-vuln Markdown “skills.” It’s a lightweight approach to converting past report history into structured heuristics and checklists for future hunting.
Have a favorite tool? Tell me.

XBOW Finds Critical Bing RCEs [📓 Blog]
by XBOW
XBOW disclosed multiple critical bugs in Microsoft infrastructure, including Bing RCEs reaching SYSTEM privileges. The disclosure underscores how high-impact issues can exist in mature public surfaces, even without exotic exploit chains.
WordPress Entra ID/Azure AD SSO Plugin Auth Bypass (CVE-2026-2628) [📓 Blog]
by YesWeHack
YesWeHack shared a write-up on CVE-2026-2628, a critical auth bypass in a WordPress Entra ID/Azure AD SSO plugin that can enable admin takeover. The post focuses on root cause and mitigation guidance for affected deployments.
Stored XSS in Jira Work Management Escalated to Org Takeover [📓 Blog]
by Imran Parray (@imranparray101)
A post describes a stored XSS in Jira Work Management with an escalation path to full organization takeover. It’s a reminder that stored client-side bugs in admin-heavy SaaS often have direct paths to privileged actions and durable access.
Magento PolyShell Pre-Auth RCE Analysis (Actively Exploited) [📓 Blog]
by Shubs (@infosec_au)
A reverse-engineering write-up covers the Magento “PolyShell” pre-auth RCE and notes active exploitation in the wild. The analysis is useful for defenders building detections and for researchers validating exposure in self-hosted Magento estates.

Python Pitfalls That Turn Into Vulns (path joins, pickle, urljoin, YAML, class pollution) [📓 Blog]
by YesWeHack
YesWeHack catalogs common Python footguns that routinely become exploitable bugs, including path-join truncation, unsafe deserialization, urljoin quirks, and insecure YAML loading. It includes concrete examples and payloads that translate well into both code review and black-box testing heuristics.
From Script Injection to Angular Supply-Chain Risk via GitHub Actions Cache Poisoning [📓 Blog]
by Adnan Khan (@adnanthekhan)
This write-up details how a small GitHub Actions script injection in Angular’s dev-infra was escalated into a supply-chain compromise path by poisoning Actions caches and stealing a bot PAT. It’s a strong case study in how CI token scope, cache behavior, and bot-driven PR workflows can combine into high-impact supply-chain exposure.
Authenticated Arbitrary File Read via Race Condition leads to 0-Click Account Take Over on n8n [📓 Blog]
by Critical Thinking Podcast
This write-up breaks down a TOCTOU race in n8n’s file handling where inconsistent symlink resolution allowed authenticated arbitrary file reads, escalating into account takeover via extracted secrets. It’s a solid blueprint for how “just file read” becomes full compromise when the target stores auth material and encryption keys locally.
Pwning .NET Framework Applications Through HTTP Client Proxies And WSDL [Blog]
by WatchTowr
A thread highlights SOAPwn research into a .NET WSDL parsing issue that can lead to arbitrary file writes in apps using ServiceDescriptionImporter, with potential RCE implications depending on write location and execution context. It’s a reminder that “legacy” SOAP toolchains still show up in modern enterprise apps.
Critical Authentication Bypass in pac4j-jwt Using Only a Public Key [📓 Blog]
by Amartya Jha
This post details CVE-2026-29000, an auth bypass in pac4j-jwt where a crafted JWE can carry an unsigned inner token that skips signature verification, enabling login as arbitrary users. It includes a full Java PoC and remediation guidance around token-type enforcement and patching.
LangSmith Chain: Internal Service Key Leak + Encoded-Slash Path Confusion [📓 Blog]
by Critical Thinking Podcast
This write-up describes a LangSmith chain where internal service JWTs leaked in responses and an encoded-slash normalization mismatch enabled access to protected internal routes. It’s a practical example of why internal auth must be tenant-scoped and why path normalization needs to be consistent at the edge and application layer.
Using LLMs for Vulnerability Research Without Losing the Plot [📓 Blog]
by Devansh (@0xasm0d3us)
This post argues that LLM-assisted vuln research works best with tight threat models and small, iterative code slices rather than “scan everything” prompts. It also discusses context-rot effects in long sessions and emphasizes validation loops to keep findings exploit-grade instead of speculative.
Starbucks SSRF: Finding Internal Hosts with Non-Resolvable Hostname Intel [📓 Blog]
by ArgosDNS.io
This write-up shows an SSRF that behaved like an HTTP proxy and became materially more impactful when paired with historical internal hostname intelligence. It demonstrates how “SSRF confirmed” can become internal service access once internal-only hostnames are discoverable and testable at scale.
Slacker Slash: Bun Path Normalization Desync Bypassed File Access Checks [📓 Blog]
by Critical Thinking Podcast
This research shows how Bun’s URL parsing and filesystem path handling can diverge, allowing string-based path checks (e.g., startsWith) to be bypassed with crafted slash patterns and sibling-prefix collisions. The PoCs illustrate why segment-aware path validation (not raw string prefixes) is required for safe file-serving middleware.
Payment Page XSS via URL Structure Tricks (userinfo + query neutralization) [📓 Blog]
by Mohamed Chadly
This write-up covers an XSS where user input was incorporated into a script src hostname, enabling attacker-controlled JS loading by abusing URL structure (userinfo and delimiter placement) rather than basic tag-breaking. It’s a strong example of why character filtering fails when the application constructs URLs/hosts from untrusted input.
Did I miss something? Tell me.

MFA Bypass via Response Tampering (Two Real-World Examples) [📓 Blog]
by Ozgur Alp
This Synack post details two MFA bypasses where client-side state and response bodies were trusted to indicate OTP success. Both cases reinforce the same lesson: OTP verification must be enforced server-side, and mutable client storage or status fields cannot be part of the trust boundary.
Automating Recon and Monitoring with n8n (Bug Bounty Workflows) [📓 Blog]
by Bugcrowd
Bugcrowd walks through using n8n to automate recon orchestration, CVE/news monitoring, and scope-change detection with toolchains like httpx/nuclei/katana. It also covers where AI nodes and MCP-style context can fit, while keeping manual validation as the final gate.
Open-Source Testing: A Bug Bounty Guide to Code Analysis [📓 Blog]
by YesWeHack
This guide covers practical approaches to OSS code analysis for bounty hunting, including how to combine SAST, fuzzing, and targeted dynamic validation. It also includes a small hands-on example to show how static findings can be turned into reproducible requests and real impact.
Cheat Sheets for XSS, CSRF, CORS, and Broken Access Control [𝕏 Tweet]
by Intigriti
Intigriti shared a thread collecting cheat sheets and methodology cards for common web bug classes, including BAC, XSS, CORS, and CSRF. It’s a quick-reference directory geared toward fast payload recall during triage and testing.
Playing with HTTP/2 CONNECT [📓 Blog]
by fl0mb
This post explores HTTP/2 CONNECT tunneling at the per-stream level and shows how multiple TCP tunnels can be multiplexed over a single HTTP/2 connection. It includes a Go implementation approach using Framer/HPACK and practical heuristics for identifying CONNECT support and proxy behavior.
Did I miss something? Tell me.

An AI Hacker Showed Me How to Exfil Data in Zero Clicks [🎥 Video]
by Ben Sadeghipour (@NahamSec)
NahamSec shares a demo-driven video on AI-assisted offensive workflows, centered on a “zero-click” style data exfiltration scenario and the assumptions that make it possible. The content focuses on how agentic automation changes recon and exploitation speed, while still requiring careful scoping and validation.
This XSS Somehow Turned Into Account Takeover! [🎥 Video]
by Medusa (@medusa_0xf)
This video demonstrates an escalation from XSS to account takeover by exfiltrating an OAuth authorization code, including WAF bypass details and an end-to-end PoC. It’s a good example of how “minor” client-side issues can become credential/token theft when OAuth flows are loosely protected.
AI’s Journey Through Zero-Days and a Thousand Bugs (XBOW Q&A) [🎥 Video]
by Bug Bounty Village
This DEF CON session covers XBOW’s multi-agent autonomous pentesting architecture, with emphasis on exploit validation to reduce hallucinations and guardrails to stay within scope. It also discusses practical limits around verification, tooling integration, and what “autonomy” looks like when platforms still require reproducible evidence.
Deeplinks, URIs, and WebViews: URI Validation Pitfalls and Consequences [🎥 Video]
by Mobile Hacking Lab
This talk breaks down deep link and WebView attack surface expansion on Android, focusing on URI validation failures that enable OAuth/intent hijacking and account takeover. It also covers WebView JavaScript interfaces as a recurring footgun for data exfiltration and file access issues.
Google VRP Report Explained: OAuth Authorization Code Leak [🎥 Video]
by Jayendran Gurumoorthy
This video reviews a Google VRP report involving an OAuth authorization code leak caused by weak origin validation logic. It walks through how an attacker could capture the code and exchange it for tokens, reinforcing the need for strict redirect/origin validation and modern OAuth hardening patterns.
3 Bugs. $0 Earned. (Bug Bounty Field Notes EP.005) [🎥 Video]
by Logan-sec (Logan-sec)
This episode walks through three validated findings that were ultimately rejected, including a legacy Strapi exposure, a dangling CNAME takeover scenario in a mobile WebView context, and a leaked API key in a JS bundle. It’s a useful look at verification steps and the practical reasons why “real bugs” still get closed out in bounty workflows.
AI Agents for Offsec with Zero False Positives (Black Hat USA 2025) [🎥 Video]
by Black Hat
This talk focuses on agent-based vuln discovery at scale, with an emphasis on exploit validators designed to eliminate false positives. It discusses architecture choices for high-confidence verification and lessons learned from large-scale testing against real applications.
Finding and Escalating S3 Misconfigurations ($5,000 Bug) [🎥 Video]
by JakSec
This video walks through identifying S3 misconfigurations and building a stronger impact narrative by validating what’s exposed and how it can be abused. It covers policies/ACLs/presigned URLs and shows how to produce report-ready evidence instead of stopping at “bucket is public.”
Did I miss something? Tell me.

Mixed-Slash Traversal Payload Bypassed Filters and a WAF [𝕏 Tweet]
by the_IDORminator (@the_idorminator)
A payload variant mixing backslashes, forward slashes, and dot segments is shared as a practical path traversal bypass against naive normalization and WAF rules. It’s a useful addition to traversal test corpuses when standard ../ patterns are blocked.
GraphQL Operation Batching Can Defeat Request-Count Rate Limits [𝕏 Tweet]
by André Baptista (@0xacb)
A reminder that some GraphQL servers accept arrays of operations in a single request, allowing high-volume login/OTP mutations without increasing request counts. This can turn “rate-limited” brute force and enumeration into a single-request problem unless rate limiting is enforced per operation.
CI/CD Artifact Output Path Traversal Can Become Runner RCE [𝕏 Tweet]
by André Baptista (@0xacb)
A thread highlights how writable pipeline definitions combined with unsanitized artifact output paths can enable file placement and code execution on CI runners. It calls out common primitives (cron, ld.so.preload, Python package shadowing) and suggests using time delays as a low-noise blind-RCE signal.
Trailing Slash and Encoding Variants as Auth/WAF Bypass Primitives [𝕏 Tweet]
by the_IDORminator (@the_idorminator)
A checklist-style reminder that trailing slashes and delimiter encodings (//, %2f, %3f, #) can flip routing and authorization behavior, or bypass brittle WAF rules. It’s particularly relevant on mixed stacks where edge routing and app routing normalize paths differently.
Fast Ways to Locate postMessage Usage in Web Apps [𝕏 Tweet]
by Intigriti
Intigriti shared a quick workflow for finding postMessage sources/sinks, including grepping bundles, using DevTools global listeners, and setting DOMWindow.message breakpoints. The tips are useful for accelerating audits of message origin validation and deserialization patterns.
One-Liner Workflow for SSRF Hunting in URL Parameters [𝕏 Tweet]
by Bugcrowd
Bugcrowd shared a compact “archive → grep → test” workflow for discovering URL-shaped parameters that are strong SSRF candidates. It’s a lightweight recon pattern that pairs well with targeted verification using redirects, DNS callbacks, and IP-encoding variants.
SSRF Tip: Alternative IP Encodings Still Bypass Weak Blacklists [𝕏 Tweet]
by drak3hft7
A reminder to test alternative IP encodings (e.g., octal forms of 127.0.0.1) when SSRF filtering relies on string blacklists. These variants often slip through allow/deny logic that doesn’t normalize before comparison.
Did I miss something? Tell me.
Because Disclosure Matters: This newsletter was produced with the assistance of AI. While I strive for accuracy and quality, not all content has been independently vetted or fact-checked. Please allow for a reasonable margin of error. The views expressed are my own and do not reflect those of my employer.